"one" radical in Chinese characters (Kangxi radical 1)Background on needs
1-SecOC Background
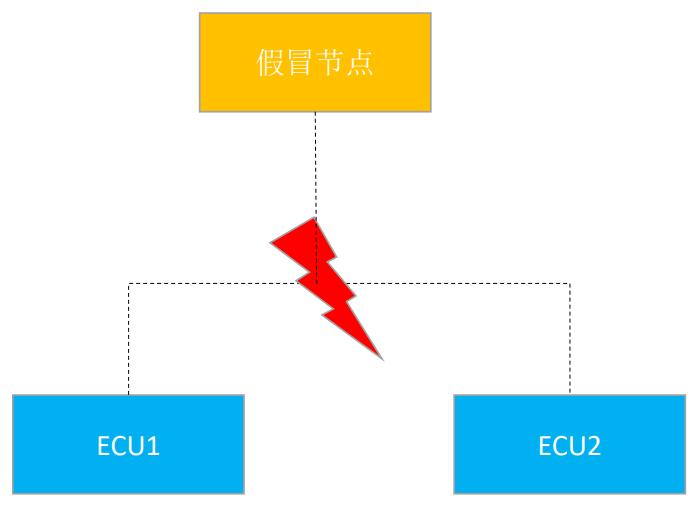
In traditional automotive electronic architectures, the in-vehicleECUlimited in number and complexity, and limited in communication bandwidth, it is considered that in-vehicleECUthat all communications between them are credible.ECUThe node will process the corresponding message as soon as it receives it. As the automotive industry and the Internet continue to evolve and cars continue to become smarter and more Internet-enabled, this default in-vehicle communication becomes increasingly insecure. If a new node is added to the vehicle's physical bus, sending fake signals or tampering with otherECUsent messages, such as accelerating, braking, and turning, while vehicle power control-relatedECUaccept the message as it is, then the vehicle will be out of control. Therefore, there is an urgent need to implement a secure and efficient algorithm to validate the message and confirm whether the sender of the message is legitimate or not and whether the data has been tampered with or not. In this case, secure on-board communication (Secure Onboard CommunicationAbbreviations SecOC) The mechanism was then born.
2-SecOC realization principle
SecOCbeSecurity Onboard Communication The abbreviation of the Chinese name is called secure in-vehicle communication.,beAUTOSARsurname CongClassic Platform 4.2A basic module was added at the beginning, and its main role is to provide authentication and protection against replay attacks for data transmission over the automotive embedded network bus.
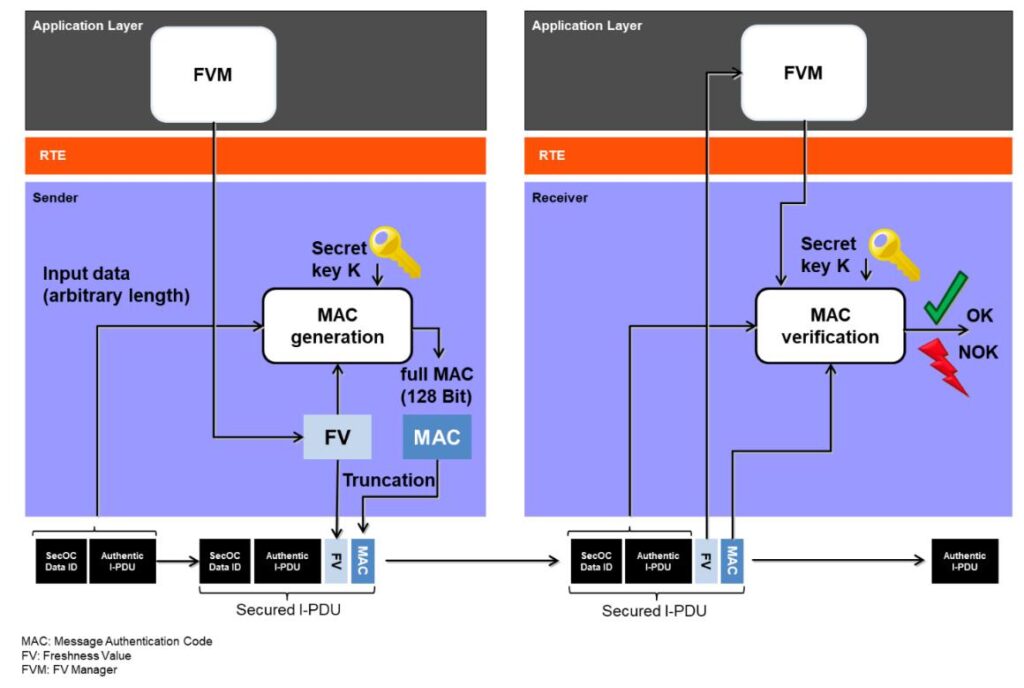
SecOC The mechanism requires that the protocol data unit (Protocol Data Unit. acronyms PDU) of the sender and receiver of the ECU All to be realized SecOC Module.
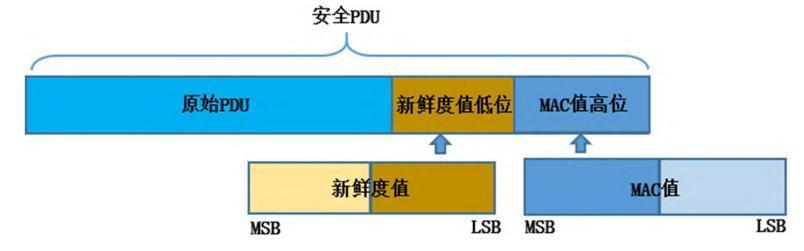
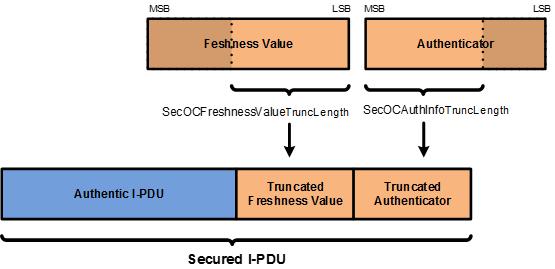
On the sender side.SecOC The module sends the protocol primitive to the protocol to be sent by sending it to the PDU Add authentication information to create securityPDU(see chart)1-2), the certification information includes the freshness value(Freshness ValueAbbreviations FV) and the information authentication code (Message Authentication CodeAbbreviations MAC).
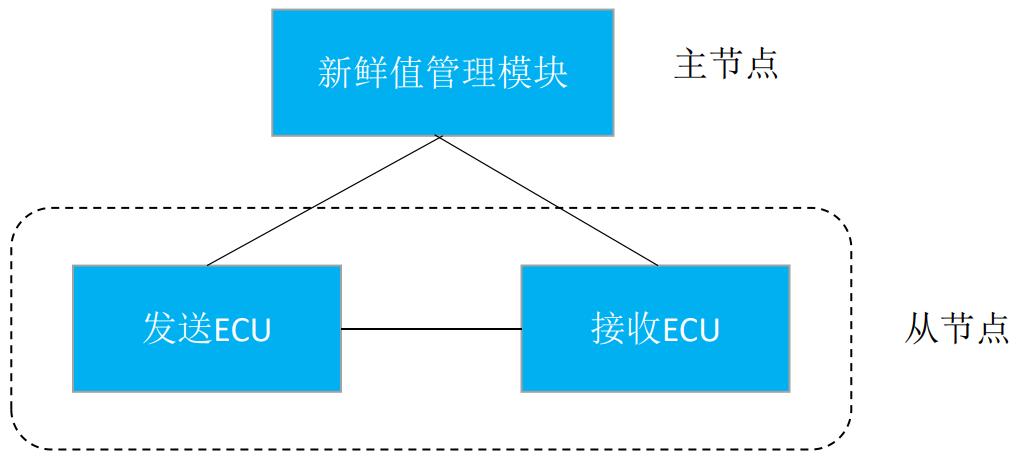
FV By Freshness Value Management Module (FVM) Get.FVM consist of Master FVM ( Acting as a gateway ) respond in singing Slave FVM( By other realizations SecOC institutional accountability ECU hold a governmental office or post ), the former sends a freshness value synchronization message to the latter to ensure that thePDU transceiver FV consistency, the latter sends the former FV Synchronization request message.
commander-in-chief (military) PDU The data identifiers, raw PDU and the complete freshness value are stitched together and passed to the authentication algorithm to produce the MAC Value.
Receiver receives security PDU postponedMACThe authentication module verifies its freshness and completeness, and if the verification is successful, then the original data will bePDUThe software module that is uploaded to the upper tier application is simply discarded if the validation fails.
stupid (Beijing dialect)Together with the star SecOC test solution
The solution is based onSecOCThe scheme realizes the authentication of sensitive information in the car.
TOSUN SecOCThe system is based onTOSUN-self-developed core softwareTSMasterrespond in singingCANThe tool can cover the testing requirements during development and production, and the main functions include master node synchronization message parsing, complete freshness value generation, calculation of theMACvalues, generates and sends security messages, receives parse-verified security messages, and fault injection functions.
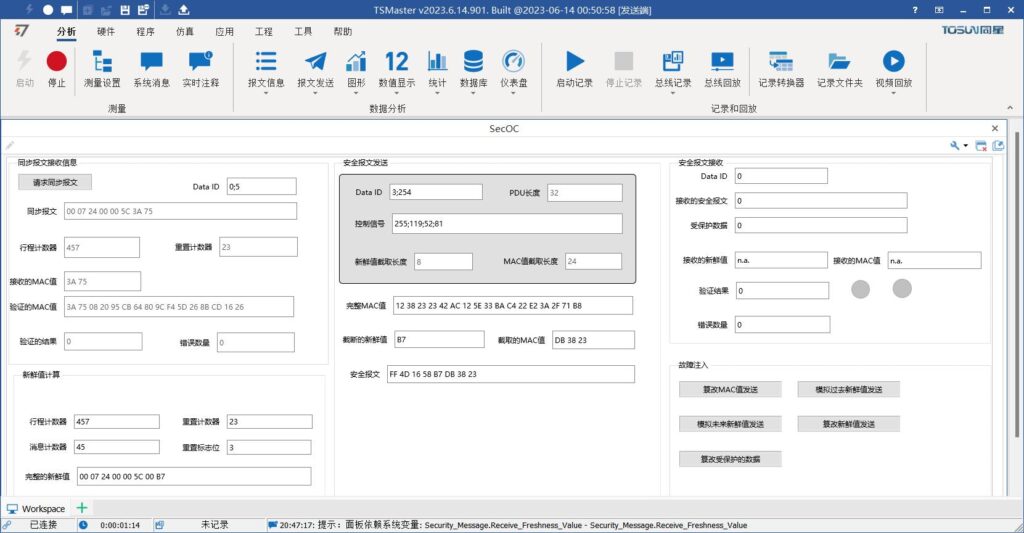
The test panel in general is shown below:
1-Synchronized message reception
The fresh value management module is generally acted by the gateway on the whole vehicle, which is responsible for sending synchronization messages to facilitate the update of fresh values from the slave nodes. The main role of the synchronization message is to ensure the securityPDUConsistency of freshness value information at the sending and receiving ends.
Trip counter for synchronization messages (Trip Counter), reset counters (Reset Counter(math.) andMACValue (Authenticator) The length is defined as follows:
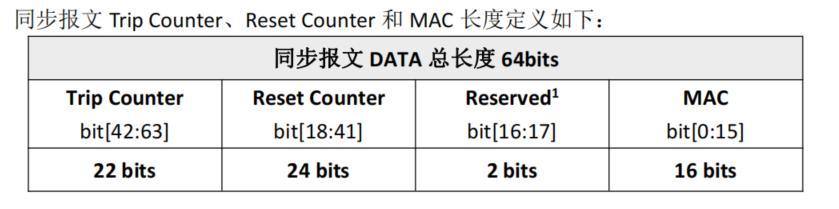
This solution utilizesAES128-CMACStandard algorithms and composites based on synchronized messagescounterFreshness Value Management Program.MACThe value is calculated asCMAC-AES128(DataID/Payload/FV, , ,CK).
Ø The illustration isTOSUN SecOCDemonstration of synchronized message reception in the solution
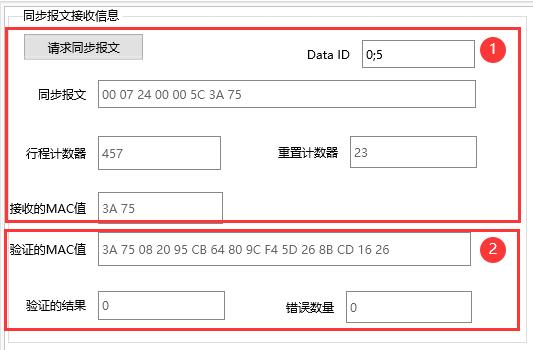
The first part displays the synchronization messages sent by the tested piece (master node) and the message parsing.Data IDBy the master node (component under test)/(Fresh Value Management Module) decision.
The second part of the algorithm calculates theMACvalue, which is the same as the value of the receivedMACThe first two values are the same, then the validation is successful return0Otherwise the validation fails to return1and number of errors+1.
2 - Freshness value management
Ø The illustration isTOSUN SecOCDemonstration of Freshness Value Management in Solutions
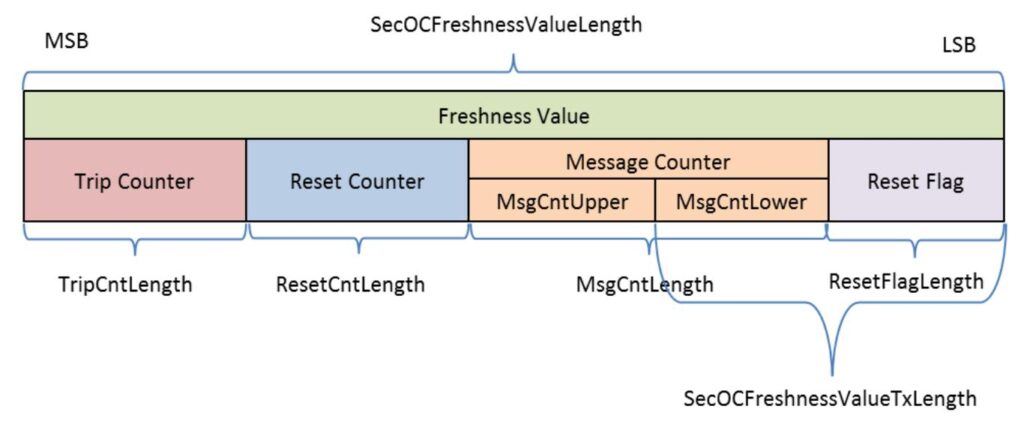
Complete freshness values include (64bit): Trip counter (Trip Counter),Reset Counter (Reset Counter), Reset flag value (Reset Flag) and the message counter (Message Counter).

1) The trip counter and reset counter are determined by the synchronization message.
2) The message counter is incremented every time a security message is sent.1.
3) The reset flag bit is the last bit of the reset counter.2bitData.
The complete freshness value within the slave node is generated from the above four data.
3-Security message sending
Ø The illustration isTOSUN SecOCDemonstration of secure messaging in the solution
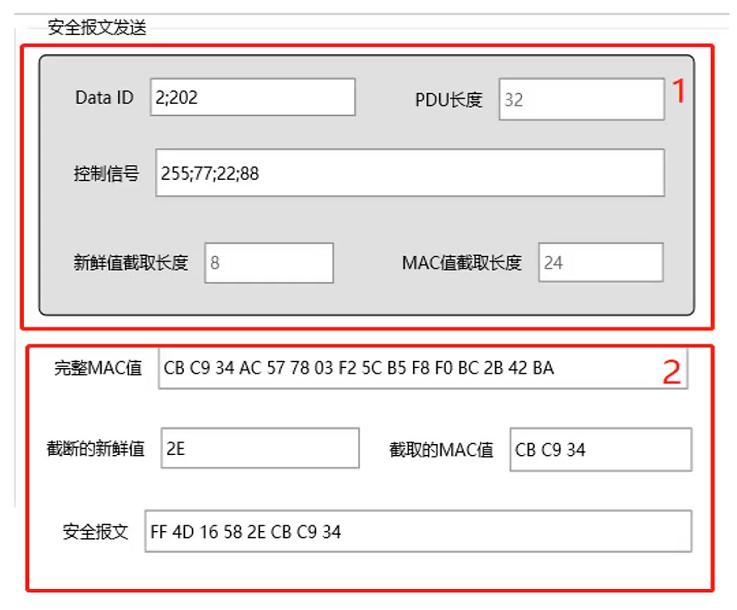
Part I Setting2byteData IDrespond in singing4Byte control signal (decimal and hexadecimal inputs are sufficient).
The second part shows the encryptedMACvalue, the fresh value of the intercept, the interceptedMACvalue and the security message sent (the security message is defined by the4byte control signal,1bytes to intercept the freshness value and3byte interceptionMAC(value composition).
The freshness value of this solution and theMACThe standard for value interception is the value of theCANprotocol in a communication mode.FVintercept low (computing)1Bytes.MACInterception of highs3Bytes.
4-Security message reception
Ø The illustration isTOSUN SecOCDemonstration of secure message reception in the solution
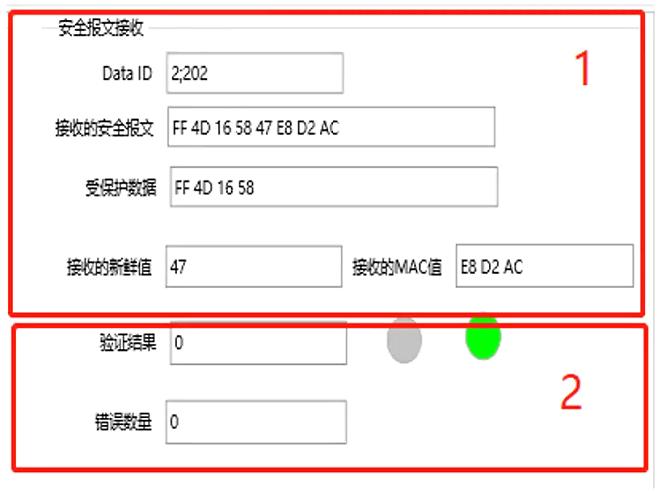
Part I Setting Up the Receiver2byteData ID(Secure Message Transmitter and Receiver Module'sData IDneeds to be consistent, otherwise it will fail to validate at the receiving end of the security message), displaying the complete security message.
The second part shows the receiving end of theMACValidation results, successful validation returns0, light green; verify failed to return1Red light on, number of errors+1.
5 - Fault Injection Test
Ø The illustration isTOSUN SecOCDemonstration of fault injection testing in a solution

Fault injection can be performed by clicking any type of fault injection button in this panel.You can see that the number of errors on the [Receiving Side] increases and lights up red. TakeTesting and evaluating the reliability and stability of the system, thus improving the quality of the system.
included among these"Simulate past fresh value send" means to change the fresh value to the fresh value of the last send, and the same applies to "Simulate future fresh value send".
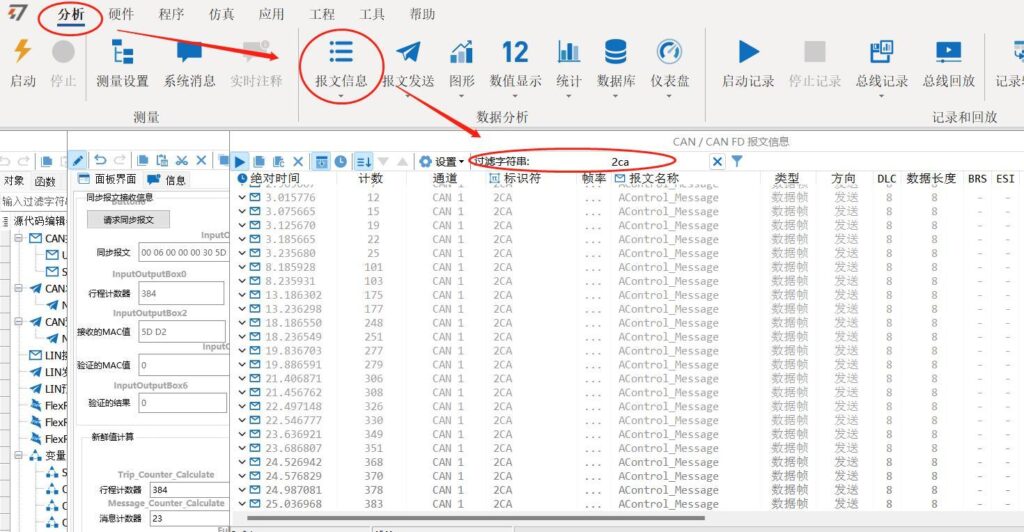
If you want to view the detailed message information, you can"Message Information" to view correctly sent or faulty injected security messages with filter identifiers of 2CA of the message is sufficient. Synchronization messages can also be viewed with the identifier 25C.




